If an adversary steals your session token, they don't need your password. They don't need your username. They don't need to bypass two-factor authentication. They already have everything a website needs to treat them as you.
And no, that's not a hypothetical. Session hijacking is a documented, widely exploited attack class, and it works precisely because of how session tokens function at a fundamental level.
A session token is a short, randomly generated string that your browser receives the moment you log in. It acts as a temporary credential, passed silently with every request you make, so the server can verify your identity without re-checking your password on each page load. Convenient by design, and such, exploitable.
This article will explain session tokens, illustrating how they work, why they are indispensable for website functionality, and the significant privacy implications they carry.
What Exactly is a Session Token?
A session token (also called a session ID) is a long alphanumeric string, generated by the server using a cryptographically secure random number generator with 128 bits of entropy or more. It acts as a temporary key and proof that you are the same authenticated user who started the session, without you having to re-enter your credentials on every page.
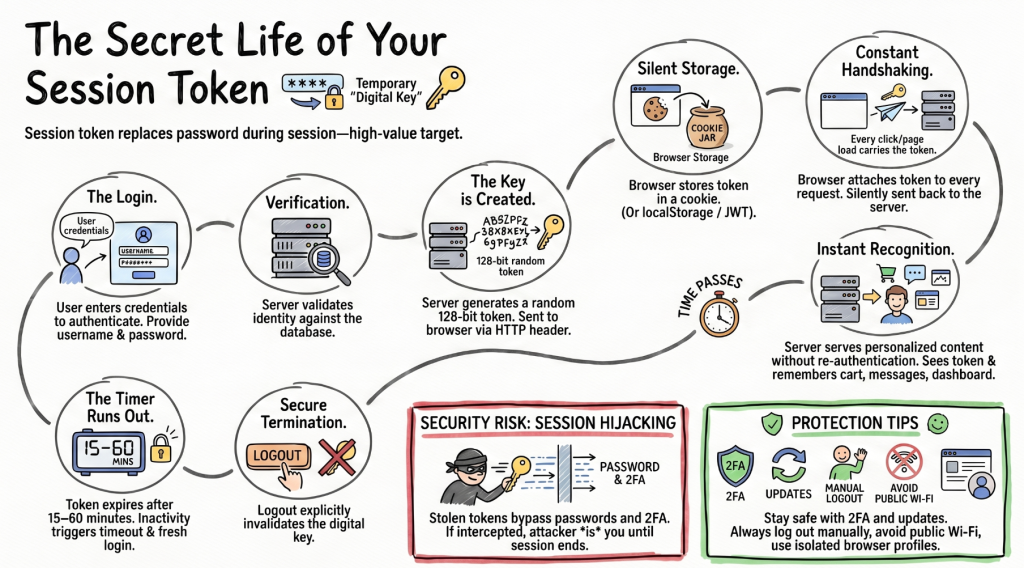
The need for tokens comes down to a fundamental limitation of the web. HTTP, the protocol browsers use to communicate with servers, is stateless, meaning each request is treated as entirely independent. The server has no built-in memory of your previous request. Session tokens solve this problem by creating a "stateful" experience, allowing the server to maintain a continuous memory of your interaction.
Here’s how it plays out in practice: After you log in to a platform for the first time, you get a session ID. Every subsequent request you make to that website (clicking a link, loading a new page, posting a comment) includes this token. The server receives the request, checks the token against its stored list, confirms it's valid and belongs to an active session, and then serves you the personalised content associated with that session—your account dashboard, your shopping cart, your private messages.
How is a Session Token Generated?
The generation of a session token is a critical security step. When a user successfully authenticates (e.g., by entering their username and password), the server generates a unique, random string of characters. This string is designed to be unpredictable and difficult to guess. The server then associates this token with the user's active session and sends it to the user's browser.
A well-generated token has four key properties:
- Uniqueness — every token is specific to one session and one user
- Randomness — generated unpredictably, not derived from user data
- Complexity — long enough to resist brute-force guessing
- Expiration — valid only for a limited time, reducing the window for misuse
Once created, the server stores the token internally and sends a copy to your browser — typically via an HTTP Set-Cookie header.
Types of Session Tokens and Their Storage

Session tokens can be implemented and stored in various ways, each with its own pros and Not all session tokens work the same way. The three most common implementations each carry distinct trade-offs.
Session Cookies
The most widespread method. The token is stored in a cookie that expires when the browser closes. Simple to implement and automatically included with every request, but vulnerable to Cross-Site Scripting (XSS) attacks if the cookie isn't properly secured with HttpOnly and Secure flags.
localStorage / sessionStorage
Modern web apps sometimes store tokens in the browser's built-in storage APIs instead of cookies. These aren't sent automatically with requests. JavaScript must retrieve and attach them manually, which can reduce certain attack surfaces but introduces others if scripts are compromised.
JSON Web Tokens (JWTs)
A more modern, stateless approach. JWTs are self-contained tokens that encode user information and are digitally signed by the server. Because all the session data lives inside the token itself, the server doesn't need to maintain a session database. The trade-off: if the signing key is ever compromised, tokens can be forged. JWTs are typically stored in localStorage and sent via the Authorization HTTP header.
How Websites Use Session Tokens to Identify You
Session tokens are the linchpin of user identification in web applications. They allow websites to distinguish between different users and maintain their specific context throughout their visit. Here's how they achieve this:
Maintaining User State
Imagine an e-commerce site. When you add an item to your cart, that information is associated with your current session. The session token ensures that when you proceed to checkout, the server knows which cart belongs to you. Without it, your cart would likely disappear with every page load.
Personalization
Websites often use session data to personalize your experience. This could include remembering your preferences, showing you recently viewed items, or tailoring content based on your past interactions within that session. The session token acts as the key to unlocking this personalized data.
Access Control
Session tokens are fundamental to implementing access control. They tell the server which resources or pages you are authorized to access. For instance, only authenticated users (those with a valid session token) can access their account dashboard or sensitive settings pages.
Preventing Session Hijacking
One of the biggest threats to session security is session hijacking, where an attacker steals a valid session token and impersonates the legitimate user. This is where techniques like browser fingerprinting become relevant. While browser fingerprinting itself doesn't directly involve session tokens, it can be used in conjunction with session management to enhance security.
Session Tokens vs. Other Tracking Mechanisms
It’s important to distinguish session tokens from other common web tracking tools:
- Persistent Cookies: These are stored on your device for a set duration (days, months, even years). They are used for long-term recognition, like remembering your login choice ("Keep me signed in") or tracking your browsing habits across sites for advertising. A session token is usually stored in a session cookie, which is designed to expire when you close your browser.
READ MORE: Why Clearing Cookies Doesn't Stop Websites From Recognizing You - Incogniton
- Browser Fingerprinting: This technique collects a suite of immutable or semi-immutable characteristics from your browser and device (screen resolution, installed fonts, OS version) to create a unique profile. Unlike a token, fingerprinting doesn't rely on data stored on your device; it's gathered live from your browser's configuration. As we've discussed in our guide on browser fingerprinting, this method is incredibly resilient against simple deletion.
- IP Address: While your IP can identify your network origin, it's often shared (by a household or office) and can change. A session token is a precise, user-specific identifier for a single, authenticated session.
- JWTs (as used beyond sessions): JWTs can be used for purposes other than session management, such as securely transmitting information between parties. When used for sessions, they function as the session token.
The clearest way to summarize the distinction is that session tokens are primarily for functional identification (keeping you logged in), whereas persistent cookies and fingerprinting are more often used for tracking identification (profiling your behaviour over time, often across different sites)
The Security Risk: Session Hijacking
Because a valid session token effectively acts as a short-term identity document, stealing one gives an attacker full access to your account, no password needed. This attack, called session hijacking, typically works by intercepting the token in transit (via unencrypted connections), extracting it from cookies using XSS exploits, or capturing it through malicious scripts.
READ MORE: What Is Session Hijacking and How Do Isolated Browser Profiles Protect Against It?
This is why well-secured websites pair session tokens with additional measures: enforcing HTTPS, setting HttpOnly cookie flags to block JavaScript access, implementing short token expiry windows, and regenerating tokens after sensitive actions like login or privilege changes.
Some platforms go further by combining session tokens with secondary signals, device metadata, behavioural patterns, or browser attributes, to detect when a valid token appears to be in use from an unusual context. This is where tools designed to manage browser environments, like Incogniton, become relevant.
Incogniton is an anti-detect browser that lets users create isolated browser profiles — each with its own cookies, local storage, and browser fingerprint — which can be useful for researchers, developers, and QA testers who need to manage multiple authenticated sessions cleanly, without cross-contamination between accounts.
Protecting Your Session Tokens

While session tokens are essential for a smooth online experience, they are also a prime target for attackers. Protecting your session tokens is paramount to safeguarding your online identity.
These are simple things you can do to protect your session tokens.
- Log Out Properly: Always use the website's designated logout function. This tells the server to invalidate your session token. Simply closing the browser doesn't always achieve this.
- Beware of Phishing: Never enter your login credentials on suspicious websites. Phishing attacks aim to steal your login details, which can then be used to obtain your session token.
- Use Strong Passwords and Two-Factor Authentication (2FA): A strong, unique password and 2FA make it much harder for attackers to gain initial access and compromise your session.
- Keep Browsers and Extensions Updated: Software updates often include security patches that protect against vulnerabilities that could be exploited to steal session tokens.
- Be Cautious with Public Wi-Fi: Public Wi-Fi networks can be less secure. Avoid accessing sensitive accounts or performing critical transactions on unsecured public networks. Consider using a VPN.
Conclusion
The web's identity layer is more layered than most users realise. Session tokens are just one thread in it, but they're one of the most important.
Without them, logging in would be meaningless; every page load would forget who you are. But they're also a window into how web tracking works at a fundamental level, and understanding them helps demystify why clearing cookies logs you out, why logout matters, and why some tracking methods survive privacy measures that target cookies alone.
For anyone managing multiple browser sessions, whether for development, testing, or account management, tools like Incogniton offer a structured way to isolate sessions and maintain clean boundaries between browser identities, without leakage between profiles.