Imagine logging into your bank account, only to watch in horror as a cursor you don’t control starts transferring your funds. This isn't a scene from a movie; it's the chilling reality of session hijacking, a cyberattack that can compromise any online account in minutes. In an era where the average person has over 100 online accounts, the attack surface for such exploits is vast.
According to recent cybersecurity reports, session-based attacks remain a top vector for data breaches, often exploiting the very mechanisms, like cookies and session tokens, that are supposed to keep us logged in and secure.
For professionals managing multiple social media, e-commerce, or advertising accounts, the risk multiplies. A single hijacked session on a platform like Facebook Ads or Shopify could lead to financial loss, data theft, and irreparable brand damage. Traditional security advice, like using strong passwords and VPNs, is no longer enough. The modern web’s architecture, designed for convenience, creates inherent vulnerabilities that savvy attackers are all too willing to exploit.
This article is a deep dive into the mechanics of session hijacking, exposing how attackers silently take over your online sessions. More importantly, we’ll explore a powerful and often overlooked defense: isolated browser profiles. By understanding and implementing this technology, you can build a formidable barrier against one of the web’s most insidious threats.
Understanding Session Hijacking: The Silent Account Takeover
Session hijacking is simply the unauthorized takeover of a user’s active session with a web application.
When you log into a website, the server doesn’t keep a constant live connection to your browser. Instead, it gives your browser a session token-a unique string of characters, often stored in a cookie-that acts as your temporary "key" for that visit. Every subsequent request you send (like loading a new page or posting a comment) includes this token, telling the server, "It’s still me."
Session hijacking occurs when an attacker steals or guesses this session token. Once in possession of it, they can impersonate you for the duration of the session, gaining full access to your account without ever needing your username or password. The legitimate user might remain logged in, completely unaware that an intruder is performing actions in their name.
How Attackers Steal Your Session

- Man-in-the-Middle (MitM) Attacks: On unsecured or compromised networks (like public Wi-Fi), an attacker can intercept the data flowing between your device and the server. If the connection isn’t encrypted with HTTPS, they can pluck session tokens right out of the air.
- Cross-Site Scripting (XSS): A malicious script is injected into a otherwise legitimate website you visit. This script can then run in your browser and steal session cookies stored there, sending them directly to the attacker.
- Session Sidejacking (Packet Sniffing): Similar to MitM, this involves using software to capture data packets on a network. Even with HTTPS, certain implementation flaws or misconfigurations can sometimes expose tokens.
- Malware: Keyloggers or specific info-stealer malware installed on your device can scan your browser’s memory or files for active session data.
- Session Fixation: Here, the attacker tricks a user into authenticating with a session ID the attacker already knows. For example, they send a link containing a predefined session ID. When the user clicks it and logs in, the attacker can use that same known ID to access the account.
The common thread is that the attack bypasses the login screen entirely. Your strong password is rendered useless because the attacker is using the key the server already trusted: your active session.
The Limitations of Conventional Browsers and Standard Security
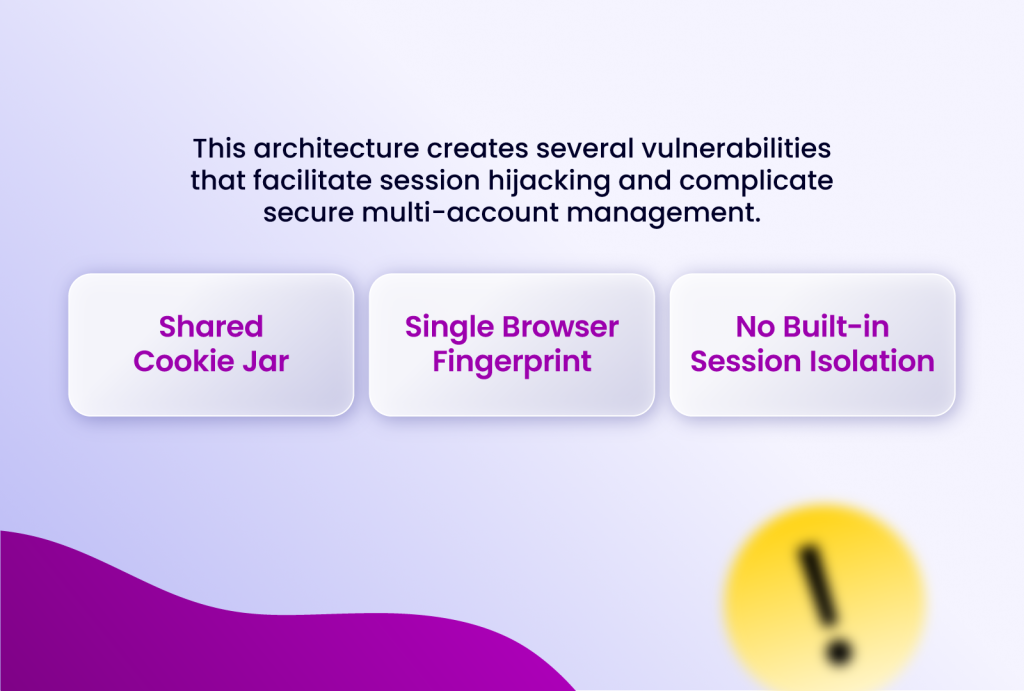
Most users rely on standard browsers like Chrome, Firefox, or Safari, which are fundamentally designed for a single user identity. This architecture creates several vulnerabilities that facilitate session hijacking and complicate secure multi-account management.
- Shared Cookie Jar: All your tabs and windows, even in private or incognito mode, to a large extent, share access to the same underlying cookie store. A malicious script in one tab (via XSS) can potentially access cookies for a completely different site open in another tab.
- Single Browser Fingerprint: Your browser broadcasts a unique combination of attributes-operating system, screen resolution, installed fonts, timezone, and more. As discussed in our guide on essential web privacy terms, this browser fingerprint is highly identifiable. If an attacker can associate a stolen session with a unique fingerprint, they can more persistently track or target that specific environment.
- No Built-in Session Isolation: There is no native mechanism to hermetically seal the session data, cookies, and cache of one website or account from another. Activity in one profile can bleed into another, creating patterns that platforms can detect and that attackers can exploit.
Furthermore, while security tools like VPNs mask your IP address, they do nothing to isolate sessions or alter your browser fingerprint. IP masking alone does not guarantee true isolation and true privacy. A hijacked session token will work regardless of the IP address it’s used from.
How Isolated Browser Profiles Create a Fortress
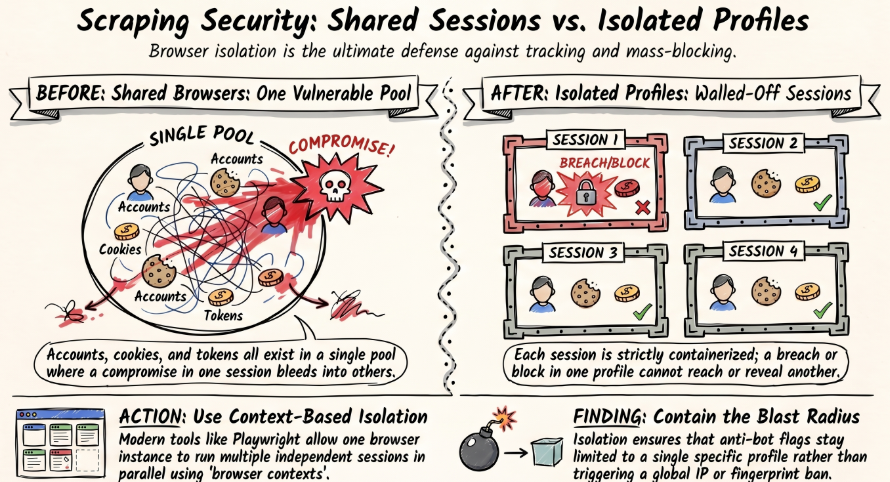
Every vulnerability described above - the shared cookie jar, the consistent browser fingerprint, the lack of session boundaries - traces back to one root problem: your standard browser treats all your activity as belonging to the same person, in the same environment, at the same time. Attackers don't need to break down your door. The architecture of conventional browsing leaves it quietly ajar.
Isolated browser profiles close that door. Permanently.
At their core, isolated profiles are independent browser sandboxes. Each one operates with its own cookie store and local storage, its own unique browser fingerprint, and its own dedicated network identity via proxy. They don't share data. They don't bleed into each other. To any website - or any attacker - each profile looks and behaves like a completely separate device, used by a completely separate person.
The security implications of this are profound.
Breaches become islands. If an attacker successfully hijacks a session in one profile, they've captured exactly that - one profile. There is no lateral movement. Your other accounts live in separate sandboxes with different cookies, different fingerprints, and often different IP addresses. The attacker has broken into one room of a building where every room has a different lock, a different key, and no connecting corridor.
XSS attacks lose their reach. Recall that cross-site scripting works by injecting a malicious script that raids your browser's cookie store. In an isolated profile, that script is trapped. It can only see the cookies belonging to that one profile's environment. Your other sessions - your ad accounts, your banking, your client platforms - are invisible to it, stored in separate vaults it cannot touch.
Accidental exposure becomes structurally impossible. For professionals managing multiple accounts, the risk isn't always a sophisticated attacker - sometimes it's the mundane reality of logging into the wrong account, or having a platform link two accounts because they detect the same browser fingerprint. Isolated profiles eliminate this by design.
Each profile maintains strict boundaries at the technical level, not just the organizational one. Your client's Facebook Ad account cannot be associated with your personal profile because, to the platform's detection systems, they don't share a single identifying attribute.
This is the shift that matters: from reactive security to structural security. A strong password is a lock you hope nobody picks. Isolated browser profiles are a fortress where each room is sealed, each identity is independent, and the compromise of one never becomes the compromise of all.
Implementing Isolation: The Role of Anti-Detect Browsers like Incogniton
While some browsers offer basic "profile" features, true isolation requires the advanced capabilities of an anti-detect browser. These tools are engineered from the ground up to create and manage these independent environments reliably.
Incogniton, for example, applies these principles directly. It allows you to "work with up to 5,000 browser profiles that do not share data or identifiers." Each profile is a fully realized, independent browser instance.
Here’s how using a tool like Incogniton directly fortifies your defenses against session hijacking:
- Per-Profile Proxy Assignment: You can attach a unique proxy to each profile. This means that even if a session token were somehow intercepted, it would be tied to a specific IP address used only for that profile. An attacker using it from a different IP might trigger security alerts.
- Fingerprint Spoofing & Management: You can customize every aspect of a profile’s fingerprint. This breaks the consistency that attackers and trackers rely on.
- Secure Team Collaboration: For teams, sharing login credentials is a major security risk. Incogniton’s browser session sharing feature allows you to grant access to a specific isolated profile without ever revealing passwords. Teammates can collaborate within the same secure environment, and you can revoke access instantly. This eliminates the need for credential sharing, a common vector for account compromise.
- Persistent, Yet Isolated, Sessions: Unlike incognito mode, profiles save cookies and cache. This is crucial for maintaining legitimate, long-lived sessions (like staying logged into an ad platform). The key is that this persistence is isolated. A persistent session in a secure, isolated profile is far safer than a persistent session in a shared, standard browser environment.
Conclusion
In the fight for online security, isolation isn’t loneliness; it’s your strongest defense.
The threat of session hijacking reminds us that security is not just about the point of entry (the password) but about protecting the entire duration of a browsing session. While traditional browsers leave us vulnerable by design, the technology to fight back is readily available.
Isolated browser profiles, as implemented in robust anti-detect browsers like Incogniton, offer a solution. They move security from a reactive stance, hoping not to get hacked, to a proactive one, where breaches are contained, and the very data attackers seek is fragmented across multiple, unrelated digital identities.
Individuals and businesses that adopt this approach can be sure that they will be able to secure their myriad online activities, collaborate safely, and operate with confidence in an increasingly perilous digital landscape.