Online privacy tool shoppers mostly ask the wrong question: they want to know which tool is better, for instance, a cloud phone or an anti-detect browser. But better at what? These two technologies don't compete; they don't even operate in the same arena.
A cloud phone lives at the telephony layer of your identity while an anti-detect browser lives at the device and behaviour layer. Conflating them is like comparing a lock to a security camera - both serve protection, but they guard completely different entry points.
This confusion has real consequences. Professionals invest in the wrong solution, leave critical vulnerabilities open, and wonder why bans keep coming.
In this article, we close that gap. You'll learn exactly what each tool does, what it cannot do, and how to build an operation that accounts for both layers properly.
What is a Cloud Phone Service?
A Cloud Phone, often called a Virtual Phone Number or VoIP (Voice Over Internet Protocol) service, is a telephone number that is not directly tied to a specific physical phone line or SIM card. It operates over the internet, allowing you to make and receive calls, send SMS texts, and sometimes use messaging apps from a web interface or software application.
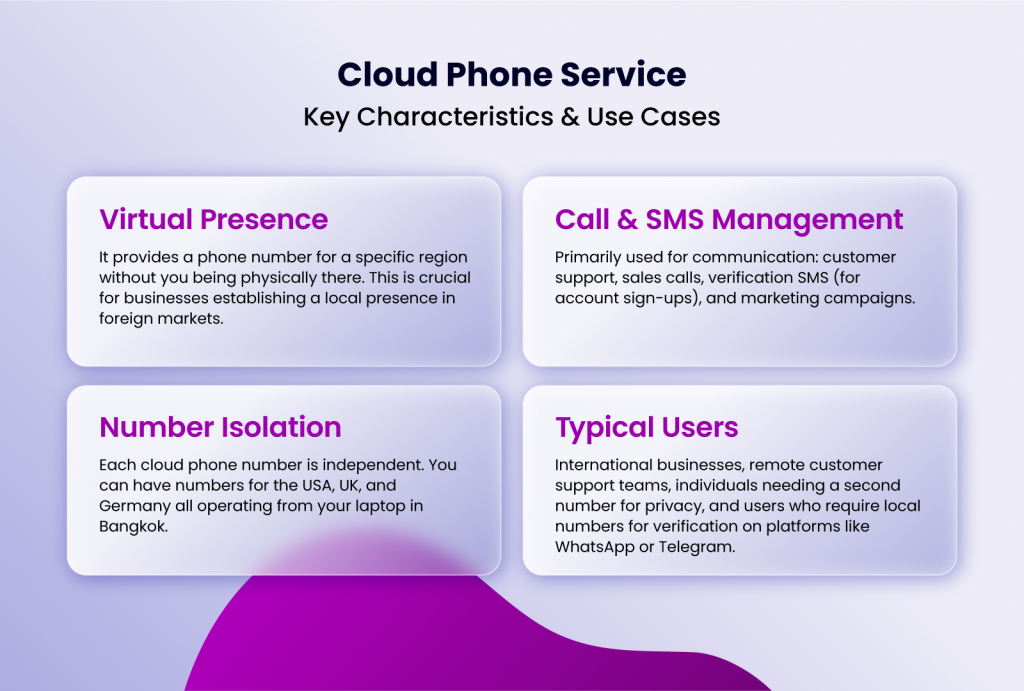
Key Characteristics & Use Cases
- Virtual Presence: It provides a phone number for a specific region without you being physically there. This is crucial for businesses establishing a local presence in foreign markets.
- Call & SMS Management: Primarily used for communication: customer support, sales calls, verification SMS (for account sign-ups), and marketing campaigns.
- Number Isolation: Each cloud phone number is independent. You can have numbers for the USA, UK, and Germany all operating from your laptop in Bangkok.
- Typical Users: International businesses, remote customer support teams, individuals needing a second number for privacy, and users who require local numbers for verification on platforms like WhatsApp or Telegram.
A cloud phone changes your telephony identity. It does not alter your browser identity.
What is an Anti-Detect Browser?
An anti-detect browser is a specialized software designed to create and manage multiple, fully isolated browser profiles. As defined in our knowledge hub, each profile has its own unique browser fingerprint (a combination of browser type, version, OS, screen resolution, fonts, etc.), separate cookies/local storage, and can be assigned a distinct IP address via proxy integration.
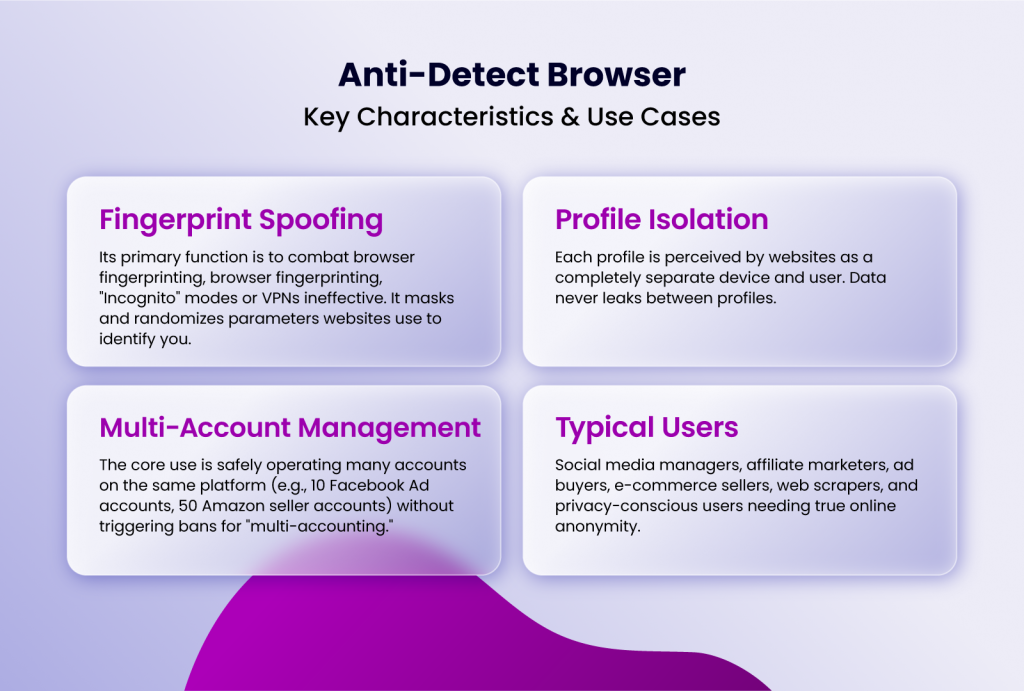
Key Characteristics & Use Cases:
- Fingerprint Spoofing: Its primary function is to combat browser fingerprinting, the advanced tracking method that makes traditional "Incognito" modes or simple VPNs ineffective. It masks and randomizes the dozens of parameters websites use to identify you.
- Profile Isolation: Each profile is perceived by websites as a completely separate device and user. Data never leaks between profiles.
- Multi-Account Management: The core use is safely operating many accounts on the same platform (e.g., 10 Facebook Ad accounts, 50 Amazon seller accounts) without triggering bans for "multi-accounting."
- Typical Users: Social media managers, affiliate marketers, ad buyers, e-commerce sellers, web scrapers, and privacy-conscious users needing true online anonymity.
In summary, a Cloud Phone gives you a new phone number. An Anti-Detect Browser gives you a new computer (from the perspective of any website you visit).
The Battle of Capabilities: A Direct Comparison
Let's break down how each tool performs in critical areas for online operations.
| Feature/Capability | Cloud Phone Service | Anti-Detect Browser (e.g., Incogniton) | Winner For... |
| Primary Purpose | Communication (Call, SMS, Verification) | Browser Activity Isolation & Multi-Account Management | Depends on the need: Talking vs. Browsing. |
| Identity Masking | Masks your real phone number. | Masks your entire browser & device fingerprint. | Anti-Detect Browser for comprehensive web identity. |
| Account Management | Can help verify accounts via SMS. | Allows safe login, browsing, and operation of multiple web accounts. | Anti-Detect Browser for ongoing web account use. |
| Platform Detection Risk | Low risk for telephony; high risk if used with same browser. | Very low risk when configured correctly (unique fingerprint + proxy per profile). | Anti-Detect Browser for web platform safety. |
| Key Strength | Establishing local presence for calls/texts. | Preventing account linkage and bans on web platforms. | Distinct and non-overlapping. |
| Typical Cost | Often per-number or per-minute SMS/call fees. | Subscription based on number of profiles/features (e.g., Incogniton starts with a free tier). | Varies by scale. |
Which Tool Do You Actually Need?
Ask yourself these questions to guide your investment:
1. What is your primary activity?
- If it's making calls, sending SMS, or verifying accounts via phone: Your primary need is a Cloud Phone. A browser alone cannot receive an SMS.
- If it's logging into websites, managing ads, posting on social media, or browsing anonymously: Your primary need is an Anti-Detect Browser. A new phone number won't stop Facebook from detecting your browser fingerprint.
2. What is the main threat you are defending against?
- If the threat is your personal phone number being linked to your activities: A Cloud Phone provides separation.
- If the threat is your browser fingerprint being tracked, leading to account bans or profiling: An Anti-detect browser is your defense. As noted in our guide on selecting an antidetect browser, advanced fingerprinting protection is the non-negotiable core feature.
3. What is the scale and complexity of your operation?
- If you need 2-3 different phone numbers: A cloud phone service is simple and cost-effective.
- If you need to manage 10, 50, or 100+ online accounts: An anti-detect browser with bulk profile creation and team features (like Incogniton) is mandatory. Cloud phones don't scale for browser management.
4. What is your budget and technical comfort?
- Cloud phones are generally straightforward: buy a number, use an app.
- Anti-detect browsers require more setup: configuring fingerprints, integrating proxies, and understanding best practices (like never reusing profiles across accounts). However, modern solutions like Incogniton have greatly simplified the user experience with intuitive dashboards and clear guides.
Practical Scenarios:
- Scenario A: A freelance graphic designer who wants a separate business phone number for client calls but uses only one Instagram and one LinkedIn account. Need: Cloud Phone only.
- Scenario B: A social media agency managing 30 different client Instagram accounts, each needing distinct posting, ad management, and analytics. Need: Anti-Detect Browser (like Incogniton) essential. Cloud phones may be needed only for initial account verification.
- Scenario C: An Amazon seller operating 5 separate storefronts in different niches to avoid policy cross-contamination. Need: Anti-Detect Browser is critical for daily operation. A cloud phone might be used once per store for verification.
Conclusion
The cloud phone vs. anti-detect browser debate isn't about choosing a winner; it's about understanding two different layers of your digital identity. Your phone number is one layer. Your browser and device fingerprint is another, far more complex and trackable layer.
For most professionals operating in the digital space, especially in marketing, e-commerce, and multi-account management, the anti-detect browser is the more fundamental and critical tool. It protects the core of your web-based activity. A cloud phone can be a useful accessory in the toolkit, often employed during the initial setup phase of the accounts you will then manage within your anti-detect browser.
By choosing the right tool for the right job, you build a secure, scalable, and efficient online operation that stays ahead of detection and thrives in the competitive digital landscape.