While the primary function of anti-detect browsers is to provide enhanced privacy and anonymity, they also serve a range of other use cases, notably market research, data collection, and marketing campaigns. However, with over 30 anti-detect browser solutions available, choosing the right one is no easy task.
This comprehensive guide explores the key factors for you to consider when evaluating an anti-detect browser, ensuring that you select a solution that aligns not only with your general requirements but also your specific needs. Let’s get to it.
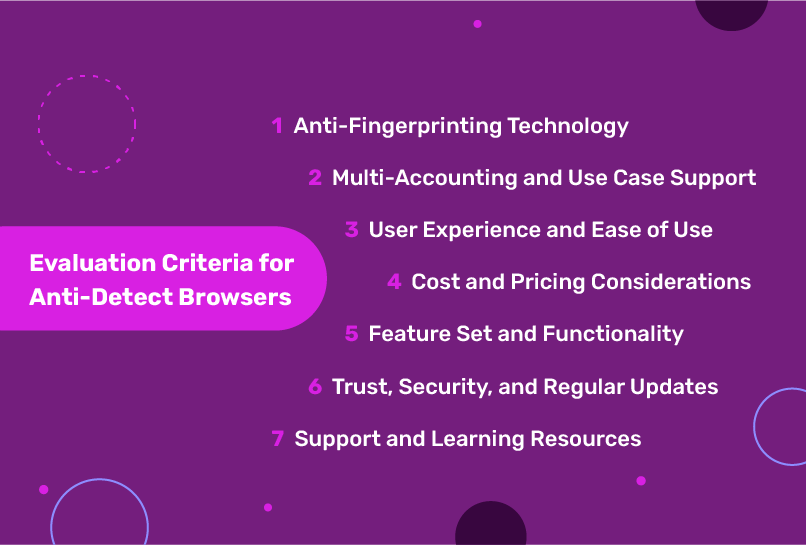
Evaluation Criteria for Anti-detect browsers
Though different users have different needs, there are still some things that are constant and underpin the effectiveness of the anti-detect browser. When assessing anti-detect browsers, these are the key criteria to consider:
-
Anti-Fingerprinting Technology
The ability to combat browser fingerprinting techniques employed by websites and online services is at the core of any effective anti-detect browser. Browser fingerprinting involves collecting and analyzing various attributes of a user’s browser, such as the user agent string, screen resolution, installed fonts and plugins, and more.
This information is then used to create a unique fingerprint that can be used to track and identify users across different websites and sessions.
Anti-detect browsers counter this by employing advanced techniques to spoof these browser attributes, creating unique, unlinkable fingerprints for each session or profile. This ensures that users can browse the web without leaving a consistent trail of digital breadcrumbs that can be used to track their activities.
Some of the key factors to consider when evaluating anti-detect browsers include:
- The granularity of control over fingerprints
The best solutions allow users to fine-tune various aspects of their browser fingerprint, such as the user agent string, screen resolution, and installed plugins. This level of control ensures that users can create highly customized and unique fingerprints tailored to their specific needs.
- Seamless Creation and Cycling of Multiple Fingerprints
Another important aspect is the ability to create and cycle through multiple fingerprints seamlessly. This feature is particularly valuable to users who need to maintain multiple online identities or conduct activities requiring constant fingerprint rotation to avoid detection.
For example, market researchers often need to gather information from various online sources without being flagged or blocked due to their activities. By cycling through multiple fingerprints, they can effectively bypass these restrictions and collect data more efficiently.
Advanced fingerprinting protection provided by anti-detect browsers enables these use cases by ensuring these users can operate seamlessly across multiple online identities without raising suspicion.
-
Multi-Accounting and Use Case Support
Many anti-detect browser use cases, such as marketing campaigns, data collection, or online research, often require the ability to create and manage multiple browser profiles or online identities simultaneously. A robust anti-detect browser solution should streamline this process, enabling users to easily spin up any number of fresh browser profiles on demand.
The ability to manage multiple profiles or accounts is critical for several reasons:
- Maintain separate online identities
Keeping separate online identities shouldn’t be reduced to “Black Hat”, as it tends to be. Users should be able to maintain their privacy and confidentiality on the web without a third party harvesting their PII, especially for professional use cases. No one wants their professional and personal lives completely interwoven.
Therefore, an antidetect browser should be able to deliver on its promise and allow users to maintain different profiles for different purposes reliably, ensuring that data and activities are compartmentalized and unlinked across profiles.
- Conduct parallel activities or experiments without cross-contamination
For instance, in the context of online marketing, advertisers may want to run multiple campaigns simultaneously, each with its own unique fingerprint and tracking mechanisms. By leveraging multiple profiles, they can isolate these campaigns and accurately measure their respective performances.
- Facilitate collaboration and teamwork
In scenarios where multiple individuals or teams are involved in a project, the ability to share and manage profiles collectively can streamline workflows and enhance productivity.
When evaluating anti-detect browsers, it’s essential to consider the ease with which users can create, switch between, and manage multiple profiles or accounts. Look for solutions that offer intuitive interfaces and streamlined processes for spinning up new profiles, as well as features that enable seamless collaboration and sharing of profiles among team members.
Additionally, consider the scalability of the solution. As your use case evolves or expands, you may require the ability to rapidly spin up and manage a large number of profiles or accounts. A robust anti-detect browser should be able to accommodate this growth seamlessly, without compromising performance or functionality.
-
User Experience and Ease of Use
While anti-detect browsers are powerful tools designed to provide advanced privacy and anonymity features, their effectiveness can be hindered if they are overly complex or difficult to use. As such, the user experience and ease of use should be a critical consideration when evaluating potential solutions.
A well-designed anti-detect browser should strike a balance between offering a comprehensive set of features and maintaining a clean, intuitive user interface. The setup process should be straightforward, allowing users to quickly and easily configure the browser to their specific needs without encountering unnecessary friction or overhead.
Some of the key processes you need to watch out for are:
- Browser download process. The simplicity of the download process is a very early sign of how much effort a team puts into the UX of an antidetect browser.
- Profile creation. The number of steps, the complexity of the required configuration, and the overall swiftness of the profile are all key here.
- Multiple profile management. Managing multiple profiles is an integral part of all anti-detect browsers, you want to look out for the user-friendliness of the process.
- Ease of collaboration. Ease of team collaboration is crucial as different team members are bound to possess varying levels of domain expertise regarding anti-detect browsers.
- Cookie management. The ability to import, export, and generate cookies when necessary is a vital metric when it comes to the browser’s UX.
- Proxy integration process. Arguably the most difficult to get right, but given that antidetect browsers work in tandem with proxies, the smoothness of proxy integration and configuration is an essential piece.
You should also consider the availability of resources and documentation to support the learning curve. Well-written guides, tutorials, and knowledge bases can significantly enhance the user experience by providing clear explanations and step-by-step instructions for navigating the browser’s capabilities.
Overall, the user experience should cater to both technical and non-technical users a
like. While power users may appreciate granular control over advanced settings and configurations, beginners should also be able to leverage the core functionality of the anti-detect browser without feeling overwhelmed.
-
Cost and Pricing Considerations
When evaluating anti-detect browsers, cost and pricing models are important factors to consider, as they can significantly impact the overall value and return on investment (ROI) for your specific use case.
Free starter plans can be an excellent opportunity to test out the core features of an anti-detect browser before committing to a paid subscription. When considering paid options, you should aim to choose a solution that not only meets your functional requirements but also provides a favorable return on investment aligned with your budget and business objectives.
A flexible pricing structure tailored to different usage levels and feature requirements is another component to look out for. This ensures that you only pay for the capabilities you need, avoiding unnecessary costs for features you may not use.
It’s also worth considering the total cost of ownership beyond just the software subscription fees. Factors such as the availability of affordable proxy packages, the need for additional hardware or infrastructure, and the potential for productivity gains or cost savings through the use of the anti-detect browser should be factored into the overall cost analysis.
-
Feature Set and Functionality
While anti-detect browsers may seem relatively straightforward on the surface, the most effective solutions pack in a wealth of productivity features that allow them to adapt to a wide variety of workflows and use cases beyond simply fingerprint spoofing.
When evaluating anti-detect browsers, it’s important to consider their overall feature set and functionality to ensure that they meet your specific needs. These features include, but aren’t limited to the following:
- Availability of collaboration tools
Availability of collaboration tools that facilitate team sharing and management of profiles. In scenarios where multiple individuals or teams are involved in a project, the ability to share and collectively manage browser profiles can streamline workflows and enhance productivity. Look for solutions that offer intuitive sharing mechanisms, access controls, and version management capabilities.
- Built-in proxy management capabilities
For users relying on proxies to further enhance their online anonymity or bypass geographic restrictions, built-in proxy management capabilities are key.
An anti-detect browser like Incogniton offers integrated proxy management tools or affordable proxy packages, allowing users to easily configure and rotate through multiple proxy servers without the need for additional third-party software.
- Automation tools
Automation is another powerful feature that can significantly enhance productivity and efficiency. Advanced anti-detect browsers may offer scripting or automation capabilities that allow users to streamline repetitive tasks or automate certain actions based on predefined rules or triggers.
This is particularly useful in scenarios involving data collection, web scraping, or repetitive testing scenarios.
- Cookie management tools
As earlier mentioned in the User experience section, cookie management is a priority in an anti-detect browser. Cookie management — generation, import, or export — helps keep your sessions natural to third-party platforms’ algorithms. Look for anti-detect browsers that offer advanced cookie management features, allowing users to easily import, export, and generate cookies from their browsing sessions.
A comprehensive and extensible feature set can future-proof your investment and ensure that the browser remains a valuable tool as your needs evolve over time.
-
Trust, Security, and Regular Updates
Given the sensitive nature of the data and activities involved in using anti-detect browsers, trust, and security should be paramount considerations when evaluating potential solutions.
The location and data practices of the company behind an anti-detect browser can significantly impact the level of trust and confidence users can place in the software.
Companies based in regions with strong data privacy regulations, such as the European Union (EU)’s General Data Protection Regulation (GDPR), may be preferable to businesses or use cases involving sensitive information or activities. These regions typically have stricter laws and guidelines governing data collection, storage, and processing, providing an additional layer of protection for user data.
When it comes to security, look for anti-detect browsers that follow industry best practices, such as
- encryption of data in transit and at rest
- regular penetration testing and vulnerability assessments, and
- prompt patching to address any identified security vulnerabilities.
These measures demonstrate a vendor’s commitment to maintaining the highest levels of security and protecting user data and systems from potential threats.
Equally important is the availability of frequent software update releases. The online landscape is constantly evolving, with new techniques and countermeasures being developed to combat browser fingerprinting and tracking.
Anti-detect browsers that receive regular updates can ensure that users have access to the latest anti-fingerprinting techniques and core browser software improvements, maintaining their effectiveness and staying ahead of potential detection methods.
-
Support and Learning Resources
While anti-detect browsers are designed to be user-friendly and intuitive, their advanced features and capabilities may involve a degree of complexity when configuring specific settings or tackling unique use cases. In such instances, reliable technical support resources can be invaluable in ensuring a smooth and successful implementation.
- The availability and responsiveness of support channels.
Look for providers that offer multiple channels, such as live chat, email, and phone support, to cater to different user preferences and urgency levels.
- Receptive and knowledgeable support staff
Delays in receiving support or inadequate responses can lead to frustration and hinder productivity. Seek out providers with dedicated support teams that have a deep understanding of their product and can provide clear, actionable guidance to resolve issues promptly.
- The availability of self-help resources
Well-crafted and comprehensive documentation, user guides, and knowledge bases can empower users to troubleshoot common issues, learn advanced features, and gain a deeper understanding of the product’s capabilities.
Look out for providers that offer detailed, up-to-date documentation covering a wide range of topics, from installation and setup to advanced configuration options and use case scenarios.
Clear, step-by-step instructions, visual aids (e.g., infographics), and video guides can greatly enhance the learning experience and make it easier for users to leverage the full potential of the anti-detect browser.
Conclusion
When you are finally ready to choose an anti-detect browser, take the time to thoroughly assess your specific needs, evaluate potential solutions against the criteria outlined in this article, and don’t hesitate to reach out to vendors for more information or to request demonstrations of their products.
Remember that different use cases may place varying levels of importance on each factor. For instance, businesses handling sensitive data may prioritize trust, security, and the vendor’s data practices, while some may place greater emphasis on user experience and ease of use.
By making an informed choice, you can unlock the full potential of anti-detect browsers, enabling you to conduct online activities with confidence, anonymity, and peace of mind, while staying ahead of the ever-evolving landscape of browser fingerprinting and tracking techniques.
FAQs
How do anti-detect browsers work to prevent browser fingerprinting?
Anti-detect browsers employ advanced techniques to spoof browser attributes like user agent strings, screen resolutions, installed fonts and plugins, and more. This creates unique, unlinkable fingerprints for each session, making it difficult for websites to track users across the web.
What security measures should I look for in an anti-detect browser?
Priority should be given to solutions that follow security best practices, such as data encryption, regular penetration testing, vulnerability monitoring, and prompt security updates. The vendor’s data practices and transparency are also important factors.
What are some common use cases for anti-detect browsers?
Anti-detect browsers are useful for a variety of purposes, including market research, data collection, online advertising and marketing campaigns, web scraping, and any other activities where maintaining anonymity and avoiding detection is crucial.
Is it legal to use an anti-detect browser?
In most regions, using an anti-detect browser for legal activities like research or analytics is permitted. However, you should review applicable laws and terms of service.
Are there any free anti-detect browser options?
Yes, many vendors offer free starter plans or trials to test out core features before committing to a paid subscription. For instance, Incogniton offers 10 free profiles for starters.
How much do paid anti-detect browser plans typically cost?
Pricing can vary but expect to pay $10-$100+ per month for advanced paid plans, depending on the features and number of profiles needed.


Comments are closed.