Cookie stuffing is one of affiliate marketing’s most notorious black-hat tactics, and one of the fastest ways to get permanently banned. With the global affiliate industry valued at over $17 billion and growing, the competition for clicks and conversions has never been fiercer. That pressure makes the temptation to cut corners very real. Some marketers resort to deceptive methods to inflate their earnings, and cookie stuffing sits at the top of that list.
This practice doesn't just violate the trust of users and advertisers—it corrodes the entire affiliate ecosystem. Platforms like Amazon Associates, ShareASale, and CJ Affiliate run sophisticated fraud detection systems that hunt for it relentlessly, and the penalty is almost always a permanent, irreversible ban.
But what exactly is cookie stuffing? How does this digital sleight of hand work under the hood, and why is it considered such a cardinal sin?
This guide is for you if you are asking these questions. Let's get to it.
What is Cookie Stuffing?
At its core, cookie stuffing is a form of affiliate fraud where an affiliate marketer illicitly places a tracking cookie on a user’s computer without their knowledge or consent, and crucially, without the user having clicked on the affiliate’s legitimate link. The goal is simple: to hijack credit for a sale that rightfully belongs to another affiliate or occurred through organic means.
Think of an affiliate cookie as a digital claim ticket. When you click a legitimate affiliate link, the merchant’s website places a cookie in your browser. This cookie contains the unique ID of the affiliate who referred you. If you purchase within the cookie’s lifespan (often 30-60 days), the affiliate earns a commission.
Cookie stuffing bypasses the "click" step entirely. The fraudster finds a way to silently load their affiliate tracking cookie onto your device, so if you later decide to buy that product through any means, even a direct Google search, their cookie might be the one that gets read, stealing the commission.
This practice is also known as "cookie dropping" or "forced clicks." It’s important to distinguish it from legitimate cookie-based tracking, which is the foundation of the affiliate industry. The illegitimacy lies in the lack of user action and transparent intent.
How Cookie Stuffing Works
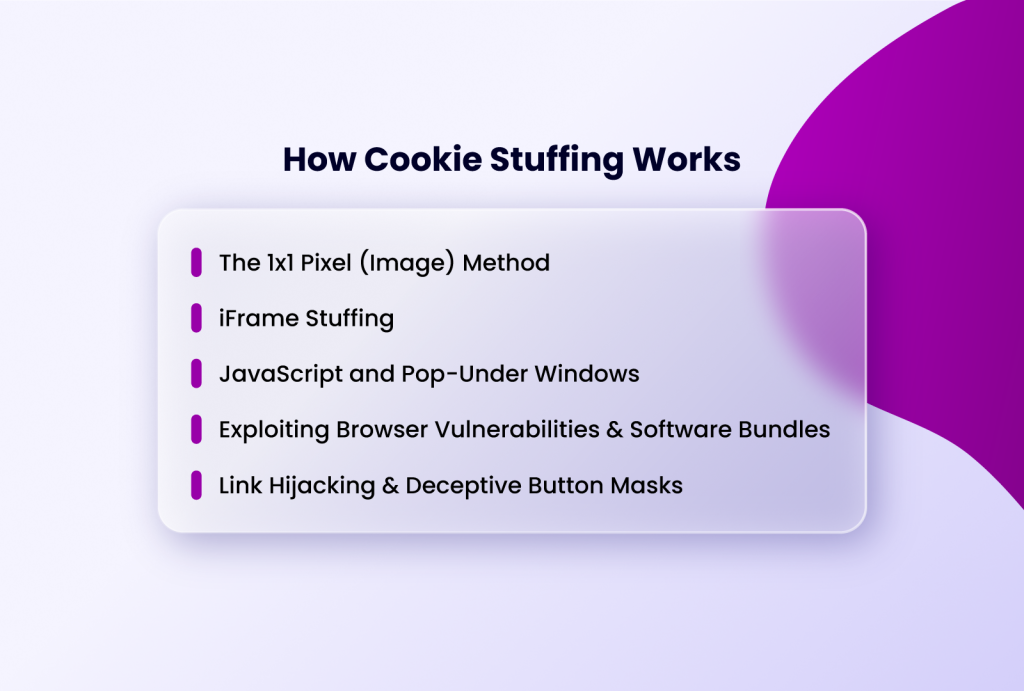
Fraudsters employ a variety of technical methods to execute cookie stuffing. These methods exploit how browsers handle web requests and cookies, often targeting vulnerabilities or using deceptive practices.
The 1x1 Pixel (Image) Method
This is one of the oldest and most common techniques. The fraudster embeds a tiny, invisible image (1 pixel by 1 pixel) on a webpage, often within an email, blog post, or forum signature. The source (src) of this image is not a picture file, but the affiliate tracking link itself. When your browser loads the page, it automatically requests that URL to "load the image," which triggers the affiliate network’s server to set the tracking cookie on your browser—all without a visible link or your interaction.
iFrame Stuffing
Similar to the pixel method, but uses an invisible HTML iframe. The iFrame loads the affiliate link in a hidden portion of the page. As the page content renders, the iFrame makes a silent request to the affiliate server, dropping the cookie.
JavaScript and Pop-Under Windows
Malicious JavaScript code can be injected into a website to trigger background processes. One variant opens a hidden "pop-under" window that loads the affiliate link, sets the cookie, and immediately closes before the user ever sees it.
Exploiting Browser Vulnerabilities & Software Bundles
More aggressive methods involve exploiting security flaws in browsers or plugins to force cookie placement. In some cases, cookie-stuffing code has been bundled with "free" software downloads, where the installer script runs the cookie-dropping routine in the background.
Link Hijacking & Deceptive Button Masks
A slightly more interactive, but still fraudulent, method involves disguising affiliate links. A button that says "Download Now" might transparently overlay an affiliate link to an online store, so a user trying to click the button inadvertently triggers the affiliate cookie.
All these methods share two traits: a lack of user intent and a deliberate effort to conceal the tracking action. The user is given no choice and is often completely unaware that an affiliate relationship is being established.
Why Cookie Stuffing is a Major Problem in Affilate Marketing

The damage caused by cookie stuffing extends far beyond the defrauded affiliate who lost a sale. It creates a cascade of negative effects across the digital marketing landscape.
- For Advertisers/Merchants: They pay commissions for sales they would have made anyway. This inflates marketing costs, distorts campaign analytics (making it impossible to know which channels are genuinely effective), and erodes trust in the affiliate channel as a whole. Resources are wasted on fraudulent payouts instead of rewarding legitimate partners.
- For Legitimate Affiliates: Honest marketers who create valuable content, build audiences, and drive genuine sales see their earnings stolen. This discourages quality work and pollutes the competitive environment.
- For Consumers: While not directly financially harmed, users' browsers are cluttered with unwanted tracking cookies without their consent, which is a violation of privacy regulations like the GDPR and CCPA. As we explored in our article on Cookies and Their Impact on Browser Profiles, cookies collect significant personal data; placing them deceptively is a serious privacy breach.
- For Affiliate Networks: Networks act as intermediaries. Widespread fraud forces them to invest heavily in complex, costly detection systems. When fraud is discovered, networks must claw back payments and ban affiliates, which is administratively burdensous and harms their reputation.
What Happens To Those Caught Cookie Stuffing
The short answer: your affiliate career ends. Networks employ forensic analytics that flag cookie stuffing reliably, and when they do, there is almost no route back. Detection typically centers on a few hard-to-fake signals. The most obvious is a wildly disproportionate conversion rate — many confirmed sales paired with almost zero legitimate clicks.
A normal affiliate has a clear trail of clicks leading to purchases; a stuffer has purchases appearing as if from thin air. Networks also watch for cookies being set suspiciously close to the moment of purchase across many unrelated users, traffic arriving from sources historically linked to pop-unders or click fraud, and occasional consumer complaints from users who spot unfamiliar domain names in their browser cookie lists.
Once flagged, the consequences are swift and compounding. The account is terminated immediately. All pending commissions, sometimes representing weeks or months of payouts, are forfeited without appeal. The affiliate is blacklisted from that network, and in most cases that information is shared across the industry, triggering bans on competing platforms simultaneously.
For cases involving large fraudulent sums, civil litigation for breach of contract or criminal fraud charges are a genuine possibility (See this case from 2014 and this one from 2025). There is no quiet exit. The networks keep the records, and the ban follows.
How to Build an Affiliate Business That Lasts Without Cutting Corners
If you want a sustainable career in affiliate marketing, avoiding black-hat tactics is non-negotiable. Here’s how to build a fraud-proof business:
Understand and Respect Network Policies
Read the Terms of Service (ToS) of every affiliate program you join. Ignorance is not an excuse. Policies explicitly forbid cookie stuffing, click fraud, and other deceptive practices. Every major network explicitly names cookie stuffing as a prohibited offense. Amazon Associates' Program Policies make clear that commissions are only earned when a customer clicks through a Special Link — any purchase that occurs outside of a genuine user-initiated click is disqualified, and violations can result in permanent termination with no appeal.
Focus on Value Creation
The most fraud-proof asset in affiliate marketing is an audience that trusts you. So invest your energy in creating high-quality content, building an engaged audience, and providing genuine recommendations.
Whether that's in-depth product reviews, comparison guides, tutorials, or niche newsletters, the format matters less than the honesty behind it. Trust compounds slowly and is lost instantly, treat it accordingly.
ALSO READ: TikTok Affiliate Marketing: A Guide to Making Money Online
Use Tools Ethically
Leverage technology to improve your efficiency, not to game the system. For example, thouse managing multiple affiliate accounts have Incogniton to help them securely and efficiently manage their accounts. They can keep each account in isolated profiles that prevent cookies ross-contamination and enusre that their operations are compliant.
Monitor Your Analytics with a Critical Eye
If your stats look too good to be true (e.g., 50 sales from 2 clicks), investigate immediately. It could be a sign you’re accidentally benefiting from a fraudster’s traffic or that your account is at risk of being flagged.
Set a baseline for what healthy conversion rates look like in your niche and flag anything that deviates significantly, in either direction. Catching anomalies early gives you the chance to clean up traffic sources and report suspicious activity before a network flags you first.
Diversify Your Income Streams
Dependence on a single affiliate program is a fragility you don't need. Programs change their commission structures, close to new affiliates, or get acquired; none of which you control. Build a portfolio of legitimate partnerships across different verticals, networks, and product types so that no single account represents your entire income.
Diversification also reduces the temptation to cut corners when one stream underperforms, because a bad month with one program doesn't threaten everything. Think of it less as spreading risk and more as building resilience into the business from the ground up.
ALSO READ: How to manage multipe eBay Accounts
Conclusion
Cookie stuffing is more than just a clever hack; it’s a fraudulent practice that steals from advertisers, harms honest affiliates, violates user privacy, and ultimately destroys the perpetrator’s career in affiliate marketing.
The affiliates who build durable, profitable businesses do so through transparency, genuine value, and tools used exactly as intended. For those managing multiple accounts and campaigns, Incogniton provides the infrastructure to operate cleanly and efficiently, without the need to cut corners that will eventually cut your career short.