Most people reach for a VPN the moment they want privacy online. It's the default answer, familiar, easy, heavily marketed. But if you're managing multiple accounts, running ad campaigns, or doing any kind of serious digital work, a VPN alone isn't enough. And using the wrong tool for the job is how accounts get flagged, banned, or linked when they shouldn't be.
VPNs, proxies, and antidetect browsers each solve a different problem. They're not competing versions of the same thing; they operate at different levels entirely.
This guide explains each tool plainly, without assuming you already know the technical details. By the end, you'll know what each one actually does, where it falls short, and how to combine them when the stakes are higher.
What a VPN Actually Does
A Virtual Private Network (VPN) is arguably the most well-known privacy tool. Its primary function is to create an encrypted tunnel between your device and a server operated by the VPN provider.
When you connect to one, your internet traffic is rerouted through the VPN provider's server. Any website you visit sees the server's IP address, not yours.
On top of that, the VPN encrypts everything passing between your device and the server. That encryption is particularly useful on public Wi-Fi, where your traffic would otherwise be easy to intercept.
Where VPNs genuinely help:
- Securing your connection on coffee shop or airport networks
- Accessing content that's region-locked (streaming libraries, blocked news sites)
- Keeping your browsing history away from your ISP
- Sometimes, bypassing throttling for specific types of traffic
Where VPNs fall short:
A VPN changes your IP address. That's it. It does nothing about your browser fingerprint — the combination of your screen resolution, browser settings, fonts, timezone, and dozens of other technical details that websites use to identify your device. Even with a VPN running, a site can recognise you across sessions just from your fingerprint.
There's also a trust issue. Every bit of your traffic passes through the VPN provider's servers. You're trusting them completely.
And if you're managing multiple accounts, a VPN doesn't help much. All your accounts still share the same exit IP address, which makes it easy for platforms to link them together.
READ MORE: VPN or an Anti-Detect Browser for My Business? - Incogniton
What a Proxy Actually Does
A proxy works similarly to a VPN at the surface level - it sits between your device and the internet, forwarding your requests through a different IP address. But that's roughly where the similarities end.
Unlike a VPN, proxies are usually configured per application (your browser, your scraping script) rather than across your whole system. And most proxies don't encrypt your traffic.
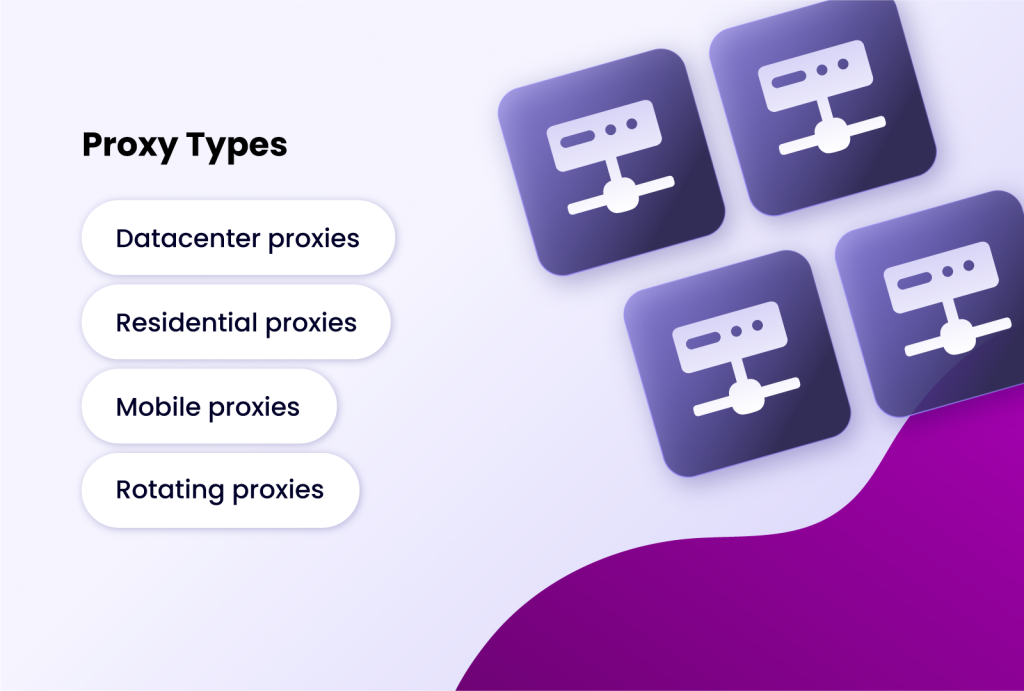
There are a few types worth knowing. For a full breakdown, see our guide on Residential IP vs. Datacenter Proxies, but here's the quick version:
- Datacenter proxies come from cloud servers. Fast and cheap, but easier for sophisticated websites to detect and block.
- Residential proxies use IP addresses assigned by real ISPs to real households. Much harder to detect, and more expensive.
- Mobile proxies use IPs from cellular networks — high legitimacy for mobile-focused tasks.
- Rotating proxies automatically cycle through a pool of IPs, either on a timer or per request. Essential for large-scale scraping.
Where proxies genuinely help:
- Web scraping and data aggregation at scale
- Checking how search results look from different locations
- Ad verification across geographic regions
- Getting around IP bans
Where proxies fall short:
Proxies only change your IP. Your browser fingerprint remains completely exposed. Like VPNs, they do nothing to protect against modern tracking methods. They're also more technically involved to set up and manage, especially rotating proxy pools.
What an Antidetect Browser Actually Does

An antidetect browser is a different category of tool entirely. It doesn't just route your traffic through a different IP — it changes the digital identity your browser presents to every website you visit.
The core problem it solves:
Modern websites don't just track you by IP address. They collect a fingerprint made up of your browser type and version, operating system, screen resolution, timezone, installed fonts, canvas rendering data, WebGL information, and more. This fingerprint can be unique enough to identify your specific device even if your IP changes.
An antidetect browser lets you control and spoof all of that. Each profile you create can have a completely different, realistic-looking fingerprint.
Profile isolation is the other major feature. Every profile operates as an independent browser — separate cookies, cache, local storage, and history. Logging into Account A on Profile 1 and Account B on Profile 2 leaves no trace connecting the two. From the platform's perspective, those are two entirely different users on two different devices.
Where antidetect browsers genuinely help:
- Managing multiple social media, ad, or e-commerce accounts without triggering "linked account" bans
- Running affiliate campaigns and ad accounts from separate, untraceable identities
- Operating multiple seller accounts on platforms like Amazon or Shopify
- Web scraping in fingerprint-unique environments when combined with proxies
- Privacy-sensitive research (journalism, competitive intelligence)
Where antidetect browsers fall short:
They only protect the browsing sessions inside them. Other apps on your system are unaffected. And to fully complete the illusion of a separate user, you still need a separate IP — which means pairing each profile with a proxy. A good antidetect browser like Incogniton has a built-in proxy manager to make this straightforward.
Running many profiles simultaneously is also resource-intensive. More profiles means more RAM and CPU.
READ MORE: Everything You Need To Know About Anti-Detect Browsers
Head-to-Head Comparison: Choosing Your Tool
| Feature | VPN | Proxy | Antidetect Browser |
| Primary Function | Encrypts traffic & masks IP at system level | Masks IP address for specific apps/tasks | Creates isolated browser profiles with unique fingerprints |
| Encryption | Yes (full tunnel) | Usually No | No (but can be combined with proxy/VPN) |
| IP Masking | Yes (single IP) | Yes (can be rotating) | No (requires proxy integration) |
| Fingerprint Spoofing | No | No | Yes |
| Best For | General privacy on public Wi-Fi, bypassing geo-blocks | Web scraping, SEO tools, task-specific IP rotation | Managing multiple accounts, avoiding platform bans, advanced privacy |
| Ease of Use | Very High (click and connect) | Medium (requires configuration) | Medium-High (profile & proxy setup) |
| Cost | Low-Monthly Subscription | Varies (pay-per-GB common for residential) | Subscription-based (per profile) |
Conclusion
Choosing between a VPN, a proxy, and an antidetect browser isn't really a choice — not if you understand what each one does. Each tool has a job. The goal is knowing which job you're trying to do, and picking accordingly.
That said, the most powerful setup for true online anonymity and operational security often involves combining these tools. Using an anti-detect browser with proxies is such a powerful combination, and you can use it for virtually any form of private and anonymous online browsing task.
For an extra layer of security, you can run the entire anti-detect browser application through a VPN connection on your machine. This encrypts the traffic between your computer and the proxy server/VPN, adding another hurdle for any local surveillance.